Deploy Service
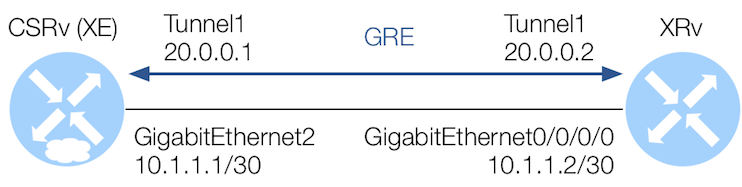
With your customer service package loaded, you can use it to deploy a service. In this simple example that is aimed at you understanding this capability, you will be deploying your simple service that will create a GRE tunnel between IOS-XE and IOS-XR devices.
Instantiate Service
-
Enter configuration mode.
conf -
Issue the command below to invoke your service providing it a name, then follow with a
?.services buildgre CSRv-XRv-GRE ?Your
?output should look similar to the below where all the parameters have to be defined.admin@ncs(config)# services buildgre CSRv-XRv-GRE ? Possible completions: check-sync - Check if device config is according to the service commit-queue - deep-check-sync - Check if device config is according to the service device1 - Tunnel Router #1 device2 - Tunnel Router #2 get-modifications - Get the data this service created log - re-deploy - Run/Dry-run the service logic again reactive-re-deploy - Reactive redeploy of service logic touch - Touch a service tunnel-dest-ip1 - Tunnel Router #2 IP Address (Destination) tunnel-dest-ip2 - Tunnel Router #1 IP Address (Destination) tunnel-inf-ip1 - Tunnel Router #1 Interface IP tunnel-inf-ip2 - Tunnel Router #2 Interface IP tunnel-inf-mask1 - Tunnel Router #1 Interface Mask tunnel-inf-mask2 - Tunnel Router #2 Interface Mask tunnel-number - Tunnel Interface ID tunnel-src-ip1 - Tunnel Router #1 IP Address (Source) tunnel-src-ip2 - Tunnel Router #2 IP Address (Source) un-deploy - Undo the effects of this service <cr> - admin@ncs(config)# services buildgre CSRv-XRv-GRE -
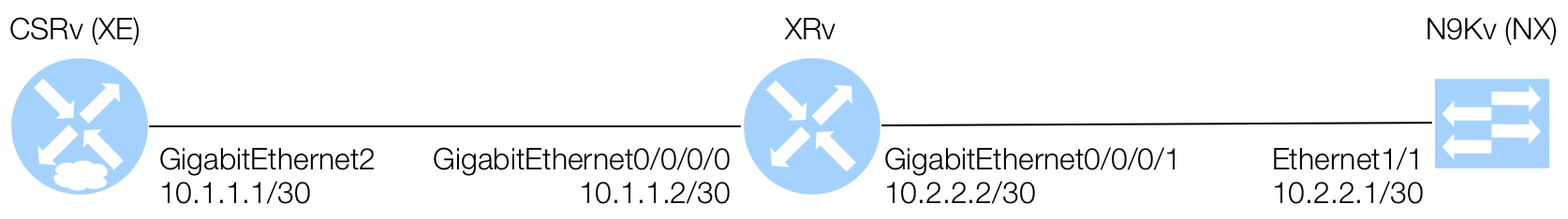
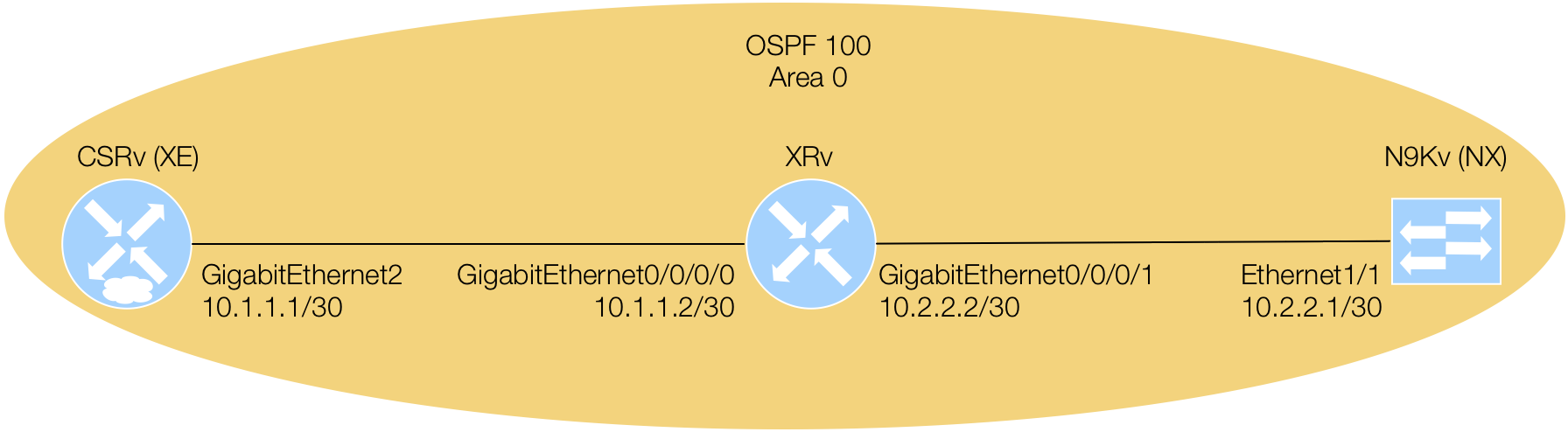
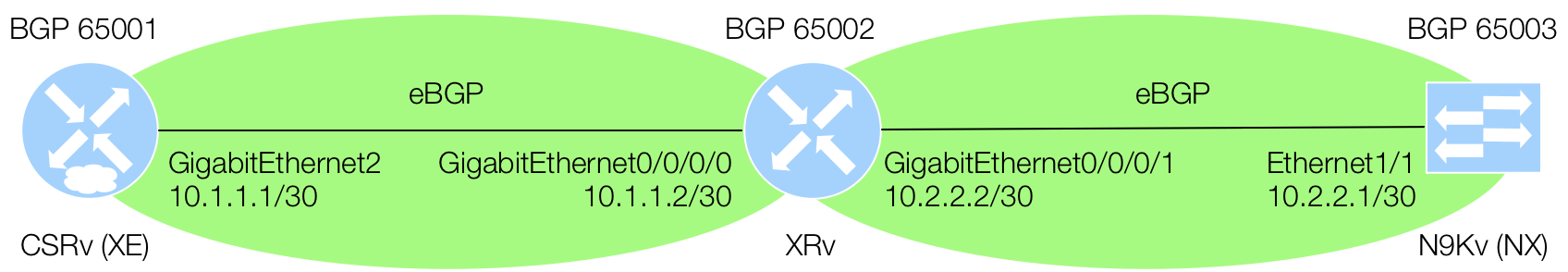
Copy the configuration line below that will instantiate your service using your physical interfaces on the XE and XR devices as the tunnel source and destinations, where your XE device is
device1and your XR device isdevice2. The tunnel addressing has to reside within the20.0.0.0network based on the pattern of the service. Your XE device will be20.0.0.1and your XR device will be20.0.0.2.services buildgre CSRv-XRv-GRE device1 CSRv tunnel-number 1 tunnel-inf-ip1 20.0.0.1 tunnel-inf-mask1 255.255.255.0 tunnel-src-ip1 10.1.1.1 tunnel-dest-ip1 10.1.1.2 device2 XRv tunnel-inf-ip2 20.0.0.2 tunnel-inf-mask2 255.255.255.0 tunnel-src-ip2 10.1.1.2 tunnel-dest-ip2 10.1.1.1 -
Before officially committing this service to deploy the configuration, lets look at two dry-run commits.
The first,
commit dry-run outformat xmlwill show the XML template populated with the configuration that is to be sent to the devices that are part of the service deployment.commit dry-run outformat xmlThe XML dry-run output should look like the below:
admin@ncs(config-buildgre-CSRv-XRv-GRE)# commit dry-run outformat xml result-xml { local-node { data <devices xmlns="http://tail-f.com/ns/ncs"> <device> <name>CSRv</name> <config> <interface xmlns="urn:ios"> <Tunnel> <name>1</name> <ip> <address> <primary> <address>20.0.0.1</address> <mask>255.255.255.0</mask> </primary> </address> <mtu>1400</mtu> </ip> <tunnel> <source>10.1.1.1</source> <destination>10.1.1.2</destination> </tunnel> </Tunnel> </interface> </config> </device> <device> <name>XRv</name> <config> <interface xmlns="http://tail-f.com/ned/cisco-ios-xr"> <tunnel-ip> <id>1</id> <mtu>1400</mtu> <ipv4> <address> <ip>20.0.0.2</ip> <mask>255.255.255.0</mask> </address> </ipv4> <tunnel> <mode> <gre>ipv4</gre> </mode> <source>10.1.1.2</source> <destination>10.1.1.1</destination> </tunnel> </tunnel-ip> </interface> </config> </device> </devices> <services xmlns="http://tail-f.com/ns/ncs"> <buildgre xmlns="http://com/example/buildgre"> <name>CSRv-XRv-GRE</name> <device1>CSRv</device1> <tunnel-number>1</tunnel-number> <tunnel-inf-ip1>20.0.0.1</tunnel-inf-ip1> <tunnel-inf-mask1>255.255.255.0</tunnel-inf-mask1> <tunnel-src-ip1>10.1.1.1</tunnel-src-ip1> <tunnel-dest-ip1>10.1.1.2</tunnel-dest-ip1> <device2>XRv</device2> <tunnel-inf-ip2>20.0.0.2</tunnel-inf-ip2> <tunnel-inf-mask2>255.255.255.0</tunnel-inf-mask2> <tunnel-src-ip2>10.1.1.2</tunnel-src-ip2> <tunnel-dest-ip2>10.1.1.1</tunnel-dest-ip2> </buildgre> </services> } } admin@ncs(config-buildgre-CSRv-XRv-GRE)#The second,
commit dry-runwill show the default, normal JSON/YANG-looking template populated with the configuration that is to be sent to the devices that are part of the service deployment.commit dry-runThe dry-run output should look like the below:
admin@ncs(config-buildgre-CSRv-XRv-GRE)# commit dry-run cli { local-node { data devices { device CSRv { config { ios:interface { + Tunnel 1 { + ip { + address { + primary { + address 20.0.0.1; + mask 255.255.255.0; + } + } + mtu 1400; + } + tunnel { + source 10.1.1.1; + destination 10.1.1.2; + } + } } } } device XRv { config { cisco-ios-xr:interface { + tunnel-ip 1 { + mtu 1400; + ipv4 { + address { + ip 20.0.0.2; + mask 255.255.255.0; + } + } + tunnel { + mode { + gre ipv4; + } + source 10.1.1.2; + destination 10.1.1.1; + } + } } } } } services { + buildgre CSRv-XRv-GRE { + device1 CSRv; + tunnel-number 1; + tunnel-inf-ip1 20.0.0.1; + tunnel-inf-mask1 255.255.255.0; + tunnel-src-ip1 10.1.1.1; + tunnel-dest-ip1 10.1.1.2; + device2 XRv; + tunnel-inf-ip2 20.0.0.2; + tunnel-inf-mask2 255.255.255.0; + tunnel-src-ip2 10.1.1.2; + tunnel-dest-ip2 10.1.1.1; + } } } } admin@ncs(config-buildgre-CSRv-XRv-GRE)# -
Offically
committhe service deployment.commitA successful commit should result in the below:
admin@ncs(config-buildgre-CSRv-XRv-GRE)# commit Commit complete. admin@ncs(config-buildgre-CSRv-XRv-GRE)# -
Verify the service deployment from within NSO:
show running-config services buildgreadmin@ncs# show running-config services buildgre services buildgre CSRv-XRv-GRE device1 CSRv tunnel-number 1 tunnel-inf-ip1 20.0.0.1 tunnel-inf-mask1 255.255.255.0 tunnel-src-ip1 10.1.1.1 tunnel-dest-ip1 10.1.1.2 device2 XRv tunnel-inf-ip2 20.0.0.2 tunnel-inf-mask2 255.255.255.0 tunnel-src-ip2 10.1.1.2 tunnel-dest-ip2 10.1.1.1 ! admin@ncs#show running-config services buildgre | tabadmin@ncs# show running-config services buildgre | tab TUNNEL TUNNEL TUNNEL INF TUNNEL TUNNEL TUNNEL TUNNEL INF TUNNEL TUNNEL NAME DEVICE1 NUMBER INF IP1 MASK1 SRC IP1 DEST IP1 DEVICE2 INF IP2 MASK2 SRC IP2 DEST IP2 ---------------------------------------------------------------------------------------------------------------------------------- CSRv-XRv-GRE CSRv 1 20.0.0.1 255.255.255.0 10.1.1.1 10.1.1.2 XRv 20.0.0.2 255.255.255.0 10.1.1.2 10.1.1.1 admin@ncs#
Verify on XE and XR CLI
-
Feel free to verify the configuration pushed by NSO on your XE and XR devices using the alias
xeandxrrespectively usingcisco.123as the password. Ensure you exit NSO first.show run int tun1 ping 20.0.0.2Pod00-CSRv#show run int tun1 Building configuration... Current configuration : 126 bytes ! interface Tunnel1 ip address 20.0.0.1 255.255.255.0 ip mtu 1400 tunnel source 10.1.1.1 tunnel destination 10.1.1.2 end Pod00-CSRv#ping 20.0.0.2 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 20.0.0.2, timeout is 2 seconds: !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 1/3/12 ms Pod00-CSRv#XR Device:
show run int tunnel-ip1 ping 20.0.0.1RP/0/RP0/CPU0:Pod00-XRv#show run int tunnel-ip1 Tue Jun 12 14:51:38.072 UTC interface tunnel-ip1 mtu 1400 ipv4 address 20.0.0.2 255.255.255.0 tunnel mode gre ipv4 tunnel source 10.1.1.2 tunnel destination 10.1.1.1 ! RP/0/RP0/CPU0:Pod00-XRv#ping 20.0.0.1 Tue Jun 12 14:51:41.210 UTC Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 20.0.0.1, timeout is 2 seconds: !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 1/4/11 ms RP/0/RP0/CPU0:Pod00-XRv#